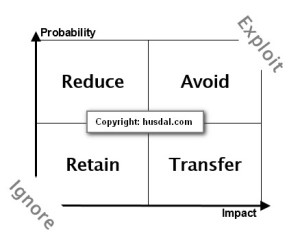
Classic risk management literature acknowledges four ways of dealing with risk after establishing a risk matrix: Avoid, Reduce, Transfer and Retain or Accept. However, as it turns out, there are six ways, not just four ways to deal with risk, as the classic risk matrix indicates. Two more are Exploit and Ignore. The former stems from Enterprise-wide Risk Management (DeLoach, 2003), while the latter is more of a sidenote in On the Value of Mitigation and Contingency Strategies for Managing Supply Chain Disruption Risks (Tomlin, 2006), but nonetheless an important observation.
Classic risk management literature acknowledges four ways of dealing with risk after establishing a risk matrix: Avoid, Reduce, Transfer and Retain or Accept. However, as it turns out, there are six ways, not just four ways to deal with risk, as the classic risk matrix indicates. Two more are Exploit and Ignore. The former stems from Enterprise-wide Risk Management (DeLoach, 2003), while the latter is more of a sidenote in On the Value of Mitigation and Contingency Strategies for Managing Supply Chain Disruption Risks (Tomlin, 2006), but nonetheless an important observation.
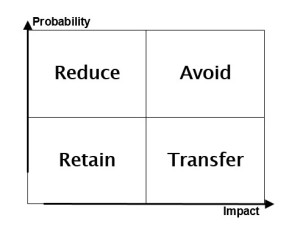
The Classic Four: Avoid, Reduce, Transfer and Retain
Classic risk management as seen in Enterprise-wide Risk Management (DeLoach, 2003) acknowledges 4 ways of dealing with risk:
- Avoid
- Reduce
- Transfer
- Retain or Accept
These four strategies can be illustrated using a risk matrix, where the impact of a certain event stemming from an exposure to a certain risk, is plotted against the probability of that event actually happening. For generic definitions of what the terms Avoid, Reduce, Transfer and Retain mean, please see my post on the ISO 73 Risk Management Vocabulary.
Naturally, high-impact high-probability risks should be avoided. High-impact low-probability risks are transferred (e.g. insurance). High-probability low-impact risks are sought to be reduced. Low-impact low-probability risks are accepted or retained. In general, as the figure implies, there are two ways of dealing with risk:
- reducing the impact of events,
by going from right to left on the x-axis - reducing the likelihood of events,
by going from the top to the bottom on the y-axix
This can be termed as contingent versus mitigative actions respectively, as I wrote about in another post. Contingent actions are actions taken after an event, to reduce the impact of an event; mitigative actions are actions taken before an event, to reduce the likelihood of an event.
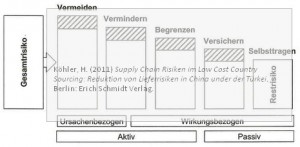
Visual: The step-by-step reduction
In a recent book I read I found another way of looking at risk management: It maintains the four classic approaches, but it does not use a risk matrix approach and it displays the steps differently.
I think that way is better in illustrating how larger risks are turned into smaller risks. Gesamtrisiko left means total or overall risk. Vermeiden means Avoid. Vermindern means Lessen, i.e. reducing probabilities. Begrenzen means Limit, i.e. reducing impacts. Versichern means Insure, i.e. transferring risks. Selbsttragen means Retain. Read more about this approach here.
Five: The Aggressive: Exploit
DeLoach (2000) Enterprise-wide Risk Management: Strategies for linking risk and opportunity also lists a fifth strategy as a possible opption: Exploit. That is, actively seeking out risk in order to gain competitive advantage, since risk per se does not always carry a negative connotation, but can also lead to beneficial results, depending on the outcome. Exploiting risk is also at the center of Lessard and Lucea (2009) Embracing risk as a core competence.
Six: The Don’t want to know about it: Ignore
Tomlin (2006), in his research, found a “see-no-evil-hear-no-evil”-strategy amongst the businesses he investigated. he discovered that many businesses willingly overlooked the risk they were exposed to, an approach he labeled Ignore, a kind of misunderstood Accept, perhaps?
Conclusion
The four strategies (Avoid, Reduce, Transfer and Retain) arising from the risk matrix are important as hands-on and easy to understand basic approaches towards dealing with risk. There’s more to risk than just avoiding risk. Adding Exploit adds the dimension of ‘positive’ risk, while adding Ignore adds a notion of unwillingness to deal with risks:
- Avoid
- Reduce
- Transfer
- Retain or Accept
- Exploit
- Ignore
Going back to figure above, both Exploit and Ignore. Exploit can be seen as the opposite of Avoid, and Ignore can be seen as a mistaken Retain.
While oversimplified, these six approaches do not show the full spectrum of risk management strategies, but they can help in setting up a basic framework for risk management. It should also be remembered that risk management needs to have both mitigative and contingent strategies.
Reference
De Loach, J. W. (2000). Enterprise-wide Risk Management: Strategies for linking risk and opportunity. London: Financial Times/Prentice Hall.
Tomlin, B. (2006). On the Value of Mitigation and Contingency Strategies for Managing Supply Chain Disruption Risks Management Science, 52 (5), 639-657 DOI: 10.1287/mnsc.1060.0515
Author link
- linkedin.com: Brian Tomlin
- linkedin.com: James W DeLoach
Related posts
- husdal.com: Enterprise-wide risk management
- husdal.com: Contingent versus mitigative
- husdal.com: ISO 73 Risk Management Vocabulary